Stop Guessing, Start Profiling
Beyond Static Rules: Proactive Security

Why Behavior Profiling is the Future of API Security
APIs are the invisible nervous system of the modern digital world. They connect our mobile applications, facilitate our financial transactions, and power the seamless digital experiences we rely on every day. But as APIs have become the foundation of modern software, they have also become the ultimate prize for malicious actors. They are no longer just pathways; they are direct pipelines to an organization’s most valuable data.
For years, the cybersecurity industry has relied on a fundamentally flawed approach to defend against these attacks: static rules. We set rate limits, block known malicious IP addresses, update blacklists, and write incredibly complex, rigid policies.

Think of traditional security like a strict bouncer at the door of a highly exclusive club. The bouncer checks your ID (your authentication token) and your point of origin (your IP address). If everything looks legitimate on the surface, the bouncer lets you in. But traditional security stops paying attention the moment you walk through the door. It doesn't care if you quietly sit at a table or try to break into the club's safe.
Modern threats have evolved past the bouncer. Today’s attackers don't try to smash through the front door with brute force. Instead, they steal a key, walk in completely undetected, and quietly exploit the business logic of your application. When an attacker perfectly mimics a legitimate user, traditional security tools are blind. They don't see a threat; they just see normal traffic.
This massive blind spot is the exact problem we set out to solve with Behavior Profiling at ApyGuard.
Moving from "Is this allowed?" to "Is this normal?"
The core philosophy behind our behavior profiling engine requires a complete shift in perspective. Instead of playing a never-ending game of cat-and-mouse—trying to predict every possible future attack and writing a specific rule against it—we focus entirely on understanding what normal looks like.
Every single application has a unique rhythm, a distinct heartbeat. Human users navigate through endpoints in specific, organic sequences. They pause, they read, they request specific amounts of data, and they interact at predictable times of the day. Bots and malicious actors, on the other hand, behave differently. They act with machine-like precision, move too quickly, or access areas of an application they have no logical reason to visit.
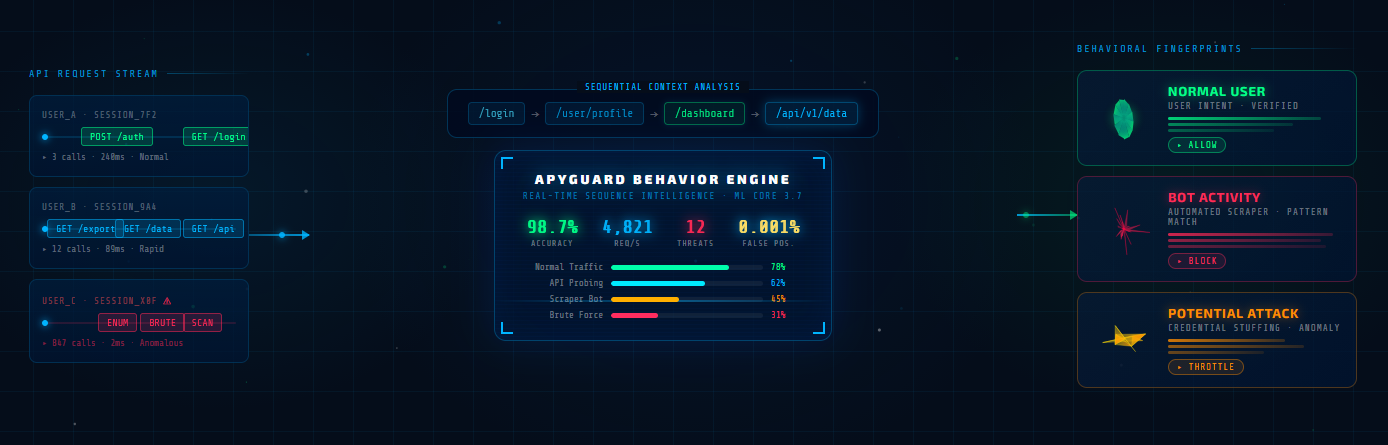
By continuously observing these complex interactions, our system doesn't just look at a single data point. It extracts multiple, overlapping "fingerprints" of your API's traffic, building a rich, multidimensional understanding of user intent.
The Baseline: Learning the Rhythm from Scratch
When our behavior profiling engine first starts observing an API, it begins with an entirely open mind. The system's baseline is a blank canvas. It makes no assumptions, applies no generic templates, and enforces no arbitrary limits.
During this crucial initial phase, it simply watches and learns. As the first comprehensive scans are completed, the canvas fills up. The engine maps out the typical, healthy habits of the system. Once it has gathered enough contextual data, it establishes a solid Baseline.
This baseline is not a static list of rules; it is a dynamic, mathematical, and deeply contextual understanding of your API's everyday life. It knows the subtle difference between a legitimate marketing campaign causing a spike in heavy usage, and a stealthy, low-and-slow data scraping attempt.
Detecting the Drift: The True Indicator of Compromise
With a comprehensive baseline established, the true power of behavior profiling kicks in. The system constantly, silently compares real-time traffic against the established norm of that specific environment.
Imagine a scenario where a legitimate user's account is compromised. The attacker logs in with perfect credentials from a clean IP address. Every traditional security check flashes green. However, the attacker suddenly begins systematically exporting sensitive data—an action the original user has never taken in their three years of using the platform.

The system instantly notices this anomaly. We call this a Drift. Even if the requests look perfectly valid on paper, the behavior is fundamentally suspicious. By catching these behavioral drifts in real-time, we can identify and mitigate zero-day attacks, sophisticated account takeovers (ATO), and subtle logic abuse long before they result in a catastrophic data breach.
The End of Alert Fatigue
One of the greatest hidden costs of static security is alert fatigue. Security teams are constantly bombarded with false positives—alerts triggered by legitimate users who accidentally tripped a poorly configured, rigid rule. This not only wastes valuable engineering time but also creates friction for real customers trying to use your product.
Because behavior profiling is rooted in context rather than rigid thresholds, it dramatically reduces this noise. It understands that a user acting slightly differently isn't always an attack, but a user fundamentally changing their nature is a red flag. It brings clarity to the chaos.
Smart Security for Dynamic Applications
Applications are living, breathing entities. They grow, they change, and they gain new features every week. Static rules are inherently rigid and require constant, manual maintenance to keep up with this growth.
Behavior profiling, by contrast, is completely dynamic. As your application evolves and your user base changes its habits, the baseline automatically adapts and learns alongside it. It requires no manual tuning, no constant rule updates, and no sleepless nights worrying if a new deployment broke a firewall rule.
Ultimately, behavior profiling at ApyGuard isn't just about blocking malicious traffic; it's about deep context. It’s about giving your APIs the intelligence to truly understand their own users. It ensures that legitimate traffic flows smoothly and without friction, while subtle, sophisticated threats are stopped dead in their tracks. It is the evolution from reactive defense to proactive intelligence.